By Susan Britt
Alabama Political Reporter
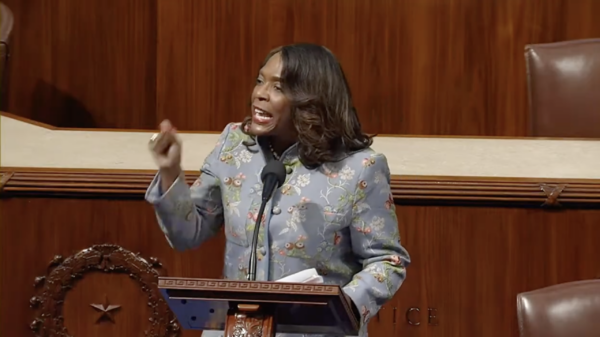
MONTGOMERY–The Alabama Digital Crimes Act passed on the House Floor on Thursday and now goes on to the Senate to be assigned to a committee.
House Bill 400 sponsored by Representative Paul DeMarco, (R-Homewood) is the companion to Senate Bill 356 carried in by Senator Cam Ward, (R-Alabaster). The Legislation is set to overhaul the criminal code in Alabama as it pertains to criminal activity committed online and through the internet.
“I am glad to see this legislation move out of the House and on to the Senate so hopefully we can get this to the Governor and finally update a law that has needed it for a long time. We have got to make sure the law stays up to date with the technology and that is what this bill does,” said DeMarco.
Alabama’s most recent computer crime bill was enacted in 1985 almost ten years before the internet was even commercially available.
In today’s cyber world computer crime encompasses a broad range of activities. Broadly, computer crimes are divided into two categories: crimes that target computers directly and crimes facilitated by computer networks or devices.
Crimes that primarily target computer networks or devices include:
Computer viruses–computer programs that can replicate themselves and spread from one computer to another. They can increase their chances of infecting other computers by infecting files on a network or network file system that is accessed my multiple individuals.
Denial-of-service attacks–(DoS attack) or distributed denial-of-service attack (DDoS attack) attempts to make a network resources unavailable to a computer. They are meant to prevent an internet site or service from functioning properly.
Malware (malicious code)–short for malicious ware, disrupts computer operation while gathering sensitive information or gaining unauthorized access to a computer. It is designed code or software whose purpose is to exploit computer or the date it contains without the consent of the owner.
Crimes that use computer networks or devices to advance other ends include:
Cyberstalking–using the internet or other electronic devices to stalk or harass individuals, groups or organizations. It includes: False accusations, monitoring, making threats, identity theft, damage to data or equipment, the solicitation of minors for sex, or gathering information in order to harass.
Fraud and identity theft–hackers design applications to invade a computer user’s private information such as credit card information, important documents and other important information for the purpose of using that information to impersonate them when transacting business. It often leaves the victim with devastating consequences.
Information warfare–closely linked to psychological warfare, it is the practice of using information technology to gain a competitive advantage over an opponent involving spreading of propaganda or disinformation to demoralize or manipulate.
Phishing scams–attempts to acquire information such as usernames and passwords and/or credit card information while impersonating a legitimate website. Typically, email and instant messaging are used to lure users to what looks like a site that would visit normally while taking them to a fake site that asks the user to enter in the information.
The Alabama Digital Crimes Act seeks to address all these areas in a comprehensive way.
Some of the areas covered by the bill are as follows:
Increase the penalty for computer tampering depending on the monetary value of the crime committed.
Create a new criminal penalty for using devices known as “skimming devices” which are used to steal information from credit cards and can re-encode that information to credit cards used by criminals.
Make it against the law to “phish,” which is using the internet to deceive, induce or fraudulently cause a person to provide confidential, identifying information which is later used for fraudulent purposes.
Expand the traditional “harassment” law to include threats made via the internet and crackdown on cyber-stalking which can include violation of a restraining order via an electronic communication.
Allow for the enforcement by subpoena and search warrant to obtain stored electronic communications from our of state service providers such as popular social media sites where cyber-harassment can occur.
Allows for a procedure to seize computer equipment that has been used to carry out a criminal offense under this act. Currently under Alabama law there is no provision to allow for the seizure of a computer used to commit a crime, so valuable evidence that can be used in a criminal case is lost.