Secretary of the Air Force Heather Wilson, just unveiled the new U.S. Air Force 2030 Science and Technology Strategy. It is an awesome, innovative, well-thought out, forward-facing, masterpiece. The 32- page report is a blue print for the next decade and beyond.
Our Air Force leaders again have made us very proud, by stating the strategies that are aligned with the National Defense Strategy, which calls for building a more lethal, resilient and rapidly and innovating Joint Force. The NDS also requires transformational strategic capabilities that must be driven by scientific and technological advances.
The executive summary mentions, great power competition is the central challenge to U.S. prosperity. A rapidly growing China and resurgent Russia, aim to coerce their regional neighbors, undermine long-standing alliances and displace American influence, from critical regions around the world. These great power competitors are challenging U.S. dominance, in all war fighting domains: air, land, sea, space, and cyberspace.
Additionally, the document covers the guiding vision of this strategy, as an Air Force that dominates time, space and complexity, in future conflicts across all operating domains, to project power and defend the homeland.
Further it reads, this means the Air Force operates at unrivaled speed. It achieves unparalleled global awareness reach and effect. It harnesses the power of complexity. Presenting the adversary with an ever-growing number of challenges, that demand resource prioritization, increase vulnerabilities and impart overwhelming confusion.
“This strategy isn’t just a list of technologies. Our approach will be to predict where adversaries cannot easily go, and make sure that the Air Force gets there first,” Wilson said.
Madam secretary added, “The advantage will go to those who create the best technologies and who integrate, and field them in creative operational ways that provide military advantages.”
As a certified information technology networking and cyberspace professional, I’m very impressed with the blue print. It also hit the nail on the head when discussing the following.
It states, the Air Force must pursue new, highly flexible, and resilient battle network technology that moves away from previous generation, hub-and-spoke connectivity, toward highly redundant mesh networks, where systems of different types can connect flexibly and automatically. Such networks will autonomously share data of different types, and classification levels across the Joint and Allied Forces.
Next the blue print mentions, they will adjust gracefully to degradation and reconfigure and change in spectrum, as needed, to maintain connectivity. Enabling research will include software-defined systems, real-time spectrum awareness, interference detection and compensation, dynamic topology management, encryption, and quantum methods for data security.
The strategy document continues, more robust satellite-based services and new position, navigation, and timing methods based on quantum science, vision-based methods, and other mechanisms must be developed. Information technology and networking must become pervasive strengths of Air Force research.
It says, the Air Force must also effectively leverage the vast capabilities and investments that exist in the commercial sector and combine them with Air Force-specific research to solve these complex challenges.
The document also mentions, the Air Force will appoint and assign a Chief Technology Officer at the Headquarters Level.
The following is just my own impromptu tutorial and lesson plan that I have used over the years in the classroom.
Just think about some of the devices that we utilize at home with a basic router or modem. At work you may have a campus or enterprise network with a wiring closet being connected through an Internet Service Provider (ISP).
Some devices that we currently utilize are desktop computers, lap tops, I Pads, Kindles cell phones, tablets, switches, routers, hubs, servers, printers, wireless access points, and firewalls. In addition, local area networks, wide area networks, cables such as copper, fiber optics, patch, straight through, console, rollover, crossover, telephone, satellite dish and cable TV. Further, wide area network interface cards, hot-swappable gigabit interface converter (GBIC) transceivers, small form-factor pluggable transceivers, drives, software, hardware, applications, personal area networks, metropolitan area networks, along with virtual software devices.
Rules, protocols and agreements must be adhered to, such as attenuation, in which guidelines have been established concerning the maximum length and effective placement distances of electrical, copper data cables, fiber optic cables and wireless radio frequency devices. If pre-defined lengths are exceeded, cable, fiber optics, radio frequencies and electricity will not operate properly.
Local area network cables for different hardware devices such as desktops, switches, routers, printers and servers are connected together with straight through or patch cables. Same type devices are joined by crossover cables. Configuration of servers, switches and routers, use console cables or KVM switches, in the wiring closet, or through remote desktops using Secure Shell or TELNET. Internet Service Provider facing, wide area network cables, WAN Interface Card (WIC), DCE or DCT side are connected to the router.
Think about some of the problems that we often face by utilizing home and office devices, such as slow network systems, in which we experience buffering and lost connections. When watching a great program on satellite TV, when inclement weather occurs, the big flat screen says, lost connection or searching for satellite, or your service will be restored in a few minutes. The service provider instructs you to push the reset button to reconnect to the network. How about when the electricity goes off and you can’t use your laptop or desktop at home or work to reach the network?
At work many of us have experienced slow networks, due to poor network design topologies, that don’t have redundancy, or automatic load-balancing.
Redundancy allows IT network engineers to place a large number of properly arranged and mesh routers to direct and move the data packets quickly through different networks; which automatically re-routes the packets through alternative routers to its destination network routers.
A layer-2 switch is utilized to move packets between the same network, primarily through the port numbers. Switches are utilized so that users on the same network may access the same printers, servers, scanners and services provided on that network.
Routers are primarily used to route packets to other networks outside your network address and IP address.
Most hubs have been replaced by switches, due to the hubs only being able to send or receive packets. Similar to a CB radio, you may send your voice message by pressing the button and speak. To listen you would release the button. If both receiver and sender press the button at the same time to speak there is a collision or no communication. With a hub, the packets will collide when senders, forward packets across the wire at the same time.
Major factors that contribute to slow networks include low-bandwidth, latency, throughput, and transmissions mediums such as fiber optics and copper cables, propagation, routers and storage devices.
Additionally, switches that have a gigabit interface converter transceiver (GBIC) that converts copper wire packets and optical highspeed light signals and vice versa may cause delays.
Further, having voice and data on the same network may create slower performance. Poorly configured voice VLANs may create jitter; where voice over internet protocols and IP phones, words may be broken into multiple parts and indistinguishable. Configuring voice and IP phones on separate virtual local area networks, and data on separate virtual local area networks will improve performance.
In closing, slow communications may occur by wrong configuration of internet facing exterior edge routers, using exterior protocols such as EBGP, EGP and BGP. Further, LAN facing routers should be configured with interior routers and interior protocols such as RIPv1, OSPF, EIGRP, IGRP and IS-IS.
Layer 3 switches can also be LAN facing and configured using interior protocols such as HSRP, VRRP and GLBP. Primarily, for redundancy and load balancing. Convergence is gained when all platforms are up and running in synchronization and in real time.
The Air Force still holds overwhelming superiority in air power and unarguable dominance in space. When adversaries can’t see Air Force planes on radar, or our smart weapon systems; they may do well to take the advice of numerous top Air Force civilian and military authorities and other wingmen.
Top American fighting men and women have strongly advised numerous adversaries to conduct their business through diplomacy with the U.S. Department of State. Foes have been further advised and warned about the consequences of fighting with the Department of Defense. Now we understand why our most recent adversaries, over the years, leave their planes on the ground. If this is not air dominance and space superiority, I don’t know what else it could be.
Our Air Force continues to make us proud. We proudly salute you!
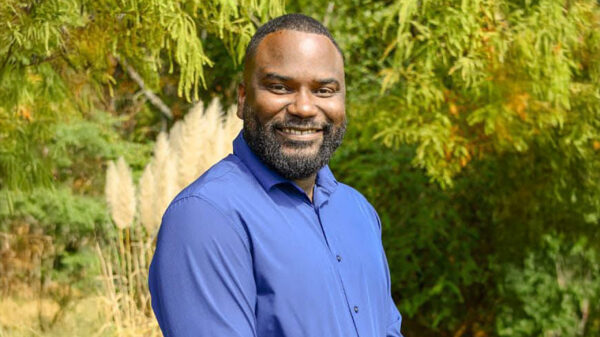
Glenn Henry is retired from the U.S. Air Force. He has been a high school teacher and university adjunct professor. He has earned numerous IT Cisco certifications. He is a Certified Professional Ethical Hacker. He lives in Montgomery with his wife Teresa.